AOC Meaning in Business: Why It Matters in SOC 2 and PCI DSS Compliance


What is AOC? AOC stands for Assertion of Compliance and is essential for businesses navigating SOC 2 and PCI DSS standards. As organizations increasingly rely on cloud service providers and third-party vendors, ensuring that these partners meet stringent compliance requirements is crucial. AOC serves as a crucial document that validates a company's adherence to security and privacy protocols, helping to build trust with clients and stakeholders. But why does it truly matter? AOC embodies a company’s commitment to safeguarding sensitive data, ensuring that both customers and regulators can have confidence in its operations. In this article, we’ll explore the significance of AOC in the context of SOC 2 and PCI DSS compliance, shedding light on the vital role it plays in risk management and operational integrity. Let’s delve into "what is AOC" and what it means for businesses striving to enhance their compliance initiatives and secure their reputations.
Why AOC?
Once a company completes PCI-DSS or SOC 2 compliance, the auditor will issue the AOC document, which the company can share with its stakeholders. The document acts as evidence of the company's commitment to maintaining robust security measures, thus ensuring the protection of sensitive data.
When dealing with third-party vendors like cloud providers, you might also need to request their Attestation of Compliance to validate the measures they have put in place to safeguard your data. The AOC acts as a bridge of trust, assuring that these external partners are compliant with necessary security standards. This, in turn, helps businesses manage their risk more effectively, ensuring that their data remains secure even when handled by external entities.
Furthermore, for your own company, an AOC plays a pivotal role in building and maintaining trust with clients. Clients and customers are more likely to engage with, and remain loyal to, companies that can prove their adherence to rigorous security standards. It is a strategic asset that enhances a company’s reputation and fosters long-term business relationships.
Overview of SOC 2 Compliance
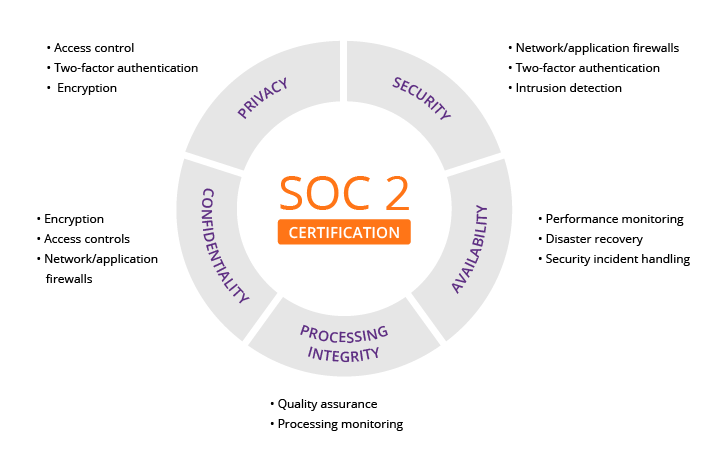
SOC 2, or System and Organization Controls 2, is a set of standards developed by the American Institute of Certified Public Accountants (AICPA) for managing customer data based on five "trust service principles": security, availability, processing integrity, confidentiality, and privacy. These principles are designed to ensure that a service organization’s systems are secure, reliable, and capable of protecting the privacy and confidentiality of the data they handle. SOC 2 compliance is particularly relevant for SAAS and cloud computing companies, as it demonstrates their commitment to maintaining high standards of data security and operational integrity.
Achieving SOC 2 compliance involves a rigorous audit process conducted by an independent third-party auditor. This audit assesses the effectiveness of a company’s internal controls and measures these against the trust service principles. The result is a detailed SOC 2 report (the AOC), which outlines the auditor’s findings and provides a comprehensive evaluation of the company’s controls. This report is invaluable for both the organization and its clients, as it offers a transparent view of the company’s security posture and control environment.
SOC 2 compliance is not a one-time achievement; it requires ongoing effort and continuous improvement. Organizations must regularly update and enhance their security controls to address emerging threats and vulnerabilities. This repetitive process ensures that the company remains compliant with SOC 2 standards and continues to provide a high level of security and reliability for its clients. The SOC 2 framework, therefore, fosters a culture of continuous improvement and proactive risk management, which is essential for maintaining trust and confidence in the digital age. Not sure if your company needs SOC 2 implementation or not? Feel free to contact us for guidance.
Overview of PCI DSS Compliance
The Payment Card Industry Data Security Standard (PCI DSS) is a globally recognized set of security standards designed to ensure the secure handling of credit card information. Developed by the Payment Card Industry Security Standards Council (PCI SSC), it applies to all entities that store, process, or transmit cardholder data. Compliance with PCI DSS is mandatory for businesses involved in credit card transactions, as it helps to prevent data breaches and protect sensitive cardholder information from unauthorized access.
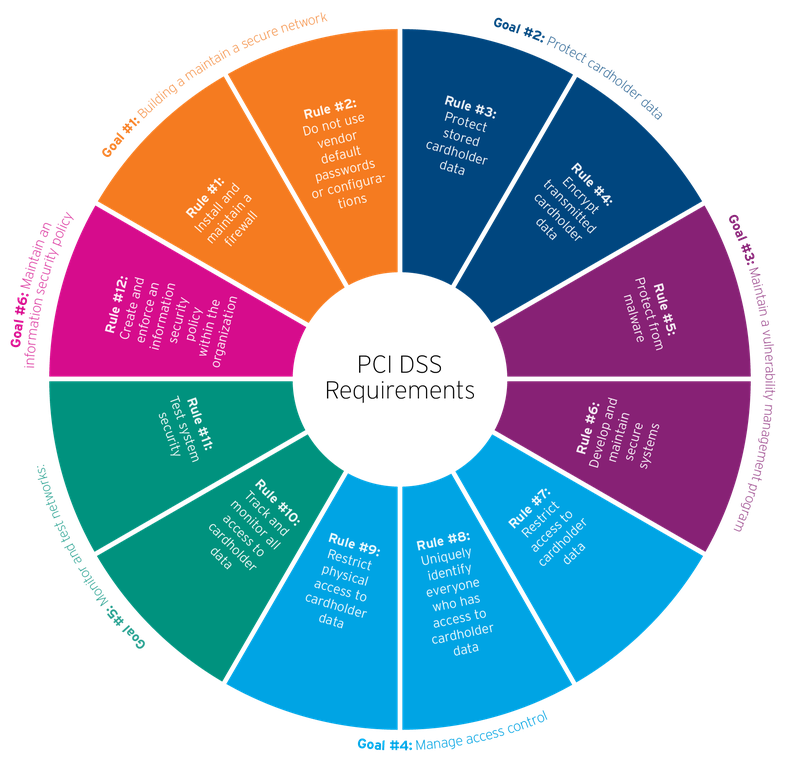
PCI DSS compliance involves a comprehensive set of requirements, including maintaining a secure network, implementing strong access control measures, regularly monitoring and testing networks, and maintaining an information security policy. These requirements are designed to create a robust security framework that protects cardholder data from a wide range of threats and vulnerabilities. Achieving PCI DSS compliance is a complex process that requires a thorough understanding of the standard’s requirements and a commitment to implementing and maintaining the necessary security controls.
The process of obtaining PCI DSS compliance typically involves a self-assessment questionnaire (SAQ) for smaller organizations and a detailed audit by a Qualified Security Assessor (QSA) for larger entities. The audit process evaluates the effectiveness of the organization’s security controls and measures these against the PCI DSS requirements. The result is a Report on Compliance (ROC) or an Attestation of Compliance (AOC), which serves as proof that the organization meets the standard’s stringent security requirements. This documentation is essential for demonstrating compliance to acquirers, payment brands, and other stakeholders.
The Role of AOC in SOC 2 Compliance
In the context of SOC 2 compliance, the Assertion of Compliance (AOC) serves as a formal declaration that an organization has successfully met the requirements of the SOC 2 audit. This document is issued by the auditor upon the completion of the SOC 2 examination and provides a summary of the audit findings.
The AOC includes key details such as the scope of the audit, the trust service principles covered, and the auditor’s opinion on the effectiveness of the organization’s controls. This information is crucial for clients and stakeholders, as it provides assurance that the organization is adhering to the highest standards of security and operational integrity.
The AOC plays a vital role in building and maintaining trust with clients and stakeholders. It serves as tangible proof of the organization’s commitment to security and compliance, helping to foster confidence in its ability to protect sensitive data. This is particularly important for service organizations that handle critical customer information, as clients need to be assured that their data is in safe hands. By providing an AOC, organizations can demonstrate their adherence to SOC 2 standards and build a strong foundation of trust with their clients.
Moreover, the AOC is an essential tool for managing risk and maintaining compliance over time. It provides a clear benchmark for the organization’s security controls and helps to identify areas for improvement. By regularly reviewing and updating the AOC, organizations can ensure that they remain compliant with SOC 2 standards and continue to provide a high level of security and reliability for their clients. This ongoing commitment to compliance is critical for maintaining trust and confidence in the organization’s operations.
The Role of AOC in PCI DSS Compliance
Like in SOC 2, for PCI-DSS compliance, the Assertion of Compliance (AOC) serves as a critical document that attests to an organization’s adherence to the PCI DSS requirements. Issued upon the successful completion of a PCI DSS audit, the AOC provides a formal declaration that the organization has met the stringent security standards set forth by the PCI Security Standards Council. This document is essential for demonstrating compliance to acquirers, payment brands, and other stakeholders, as it provides assurance that the organization is taking the necessary steps to protect cardholder data.
The AOC is a key component of the PCI DSS compliance process, as it provides a comprehensive overview of the organization’s security posture. It includes important details such as the scope of the audit, the PCI DSS requirements covered, and the auditor’s findings. This information is crucial for stakeholders, as it provides a clear and transparent view of the organization’s compliance status. By providing an AOC, organizations can demonstrate their commitment to maintaining a high level of security and protecting sensitive cardholder information.
Furthermore, the AOC plays a vital role in managing risk and maintaining compliance over time. It serves as a benchmark for the organization’s security controls and helps to identify areas for improvement. By regularly reviewing and updating the AOC, organizations can ensure that they remain compliant with PCI DSS standards and continue to provide a high level of security for their customers. This ongoing commitment to compliance is essential for maintaining trust and confidence in the organization’s ability to protect sensitive data.
Key Components of an AOC
An Assertion of Compliance (AOC) document typically includes several key components that provide a comprehensive overview of an organization’s compliance status. This components includes:
- The scope of the audit: This outlines the systems, processes, and data that were assessed during the compliance evaluation. This information is crucial for stakeholders, as it provides a clear understanding of the areas that were covered and ensures that the audit was thorough and comprehensive.
- The auditor’s opinion: This provides an assessment of the effectiveness of the organization’s security controls. This section includes the auditor’s findings and conclusions, as well as any areas for improvement that were identified during the audit. The auditor’s opinion is a critical part of the AOC, as it provides an independent and objective evaluation of the organization’s compliance status.
- Summary of the organization’s compliance: Compliance with the relevant standards, such as SOC 2 or PCI DSS. This section provides a detailed overview of the specific requirements that were met and any exceptions or deviations that were identified. This information is essential for stakeholders, as it provides a clear and transparent view of the organization’s compliance status and helps to build trust in its security practices.
How to Obtain an AOC
We at Regulance make this easy for you through our compliance management solution so that you don't have to dig into multiple guides and documents to figure things out.
Obtaining an Assertion of Compliance (AOC) involves a multi-step process that begins with a thorough understanding of the relevant compliance standards. Organizations must first familiarize themselves with the requirements of the standards they are seeking to comply with, such as SOC 2 or PCI DSS. This involves reviewing the specific criteria and ensuring that their systems, processes, and controls align with these requirements.
The next step in obtaining an AOC is to conduct a comprehensive internal assessment to identify any gaps or areas for improvement. This involves reviewing the organization’s existing security controls and comparing them against the compliance standards. Any deficiencies identified during this assessment should be addressed and remediated to ensure that the organization meets the necessary requirements.
Once the internal assessment is complete, the organization must engage an independent third-party auditor to conduct a formal compliance audit. The auditor will evaluate the organization’s controls and processes against the relevant standards and provide a detailed report of their findings. If the organization meets the requirements, the auditor will issue an AOC, which serves as formal proof of compliance. This document is essential for demonstrating compliance to stakeholders and maintaining trust in the organization’s security practices.
Common Challenges in AOC Acquisition
Acquiring an Assertion of Compliance (AOC) can be a challenging process, and organizations often face several common obstacles.
- Complexity of compliance frameworks: Both SOC 2 and PCI DSS have detailed and stringent requirements that can be difficult to understand and implement. Organizations must invest significant time and resources in understanding these standards and ensuring that their controls and processes align with the requirements.
- Continuous improvement and ongoing compliance: Compliance is not a one-time achievement; it requires ongoing effort and continuous monitoring to ensure that the organization remains compliant. This can be particularly challenging for organizations that lack the necessary resources or expertise to maintain compliance over time. Regularly reviewing and updating security controls, conducting internal assessments, and staying informed of changes to the compliance standards are essential for maintaining ongoing compliance.
- Third-party vendors and service providers' risks: As organizations increasingly rely on external partners for various services, ensuring that these third parties meet the necessary compliance requirements becomes a critical concern. Managing and monitoring the compliance status of these external partners can be complex and time-consuming. Organizations must establish clear expectations and processes for third-party compliance and ensure that they have the necessary visibility and control to manage these relationships effectively.
Best Practices for Maintaining Compliance
Maintaining compliance with SOC 2 and PCI DSS standards requires a proactive and continuous approach.
- Automate the processes: One of the best practices is to automate the processes, i.e., continuous monitoring through a compliance management solution like Regulance. Regulance has configured all you need to maintain your SOC 2 and PCI DSS. This includes, and not limited to, risk assessments, vendor management, experts and auditors support, penetration tests, evidence gathering, and so much more.
- Conduct regular internal assessments and audits: To identify any gaps or areas for improvement. These assessments should be thorough and comprehensive, covering all relevant systems, processes, and controls. Any deficiencies identified during these assessments should be addressed promptly to ensure that the organization remains compliant. Regular audits also help to identify emerging threats and vulnerabilities, enabling the organization to take proactive measures to mitigate these risks.
- Engaging with third-party experts: Engaging with experts and leveraging external resources can also be beneficial for maintaining compliance. Independent auditors, consultants, and compliance experts can provide valuable insights and guidance on best practices and emerging trends. These external resources can help organizations stay informed of changes to the compliance standards and ensure that their controls and processes remain effective.
Conclusion: The Future of AOC in Compliance Standards
As the field of cybersecurity and compliance continues to evolve, the importance of the Assertion of Compliance (AOC) is likely to grow. With increasing reliance on cloud-based solutions, third-party vendors, and complex digital ecosystems, the need for robust and transparent compliance documentation will become even more critical. AOCs will continue to serve as a vital tool for building trust and ensuring that organizations meet the stringent security and privacy standards required to protect sensitive data.
The future of AOC in compliance standards will also be shaped by advancements in technology and automation. As organizations seek to streamline their compliance efforts and reduce the burden on internal resources, leveraging compliance automation tools and technologies will become increasingly important. These tools can help organizations manage and monitor their compliance status more effectively, providing real-time insights and enabling proactive risk management.
Ultimately, the role of the AOC in compliance standards will continue to be essential for demonstrating an organization’s commitment to security and operational integrity. By understanding the significance of the AOC and implementing best practices for maintaining compliance, organizations can enhance their security posture, build trust with clients and stakeholders, and ensure the protection of their information assets. The AOC is not just a compliance requirement; it is a strategic asset that will play a crucial role in the future of cybersecurity and compliance.
Talk to our experts today for free support and guidance.