What Does It Really Take to Achieve FedRAMP Authorization?


Introduction
If you're a cloud service provider with ambitions to work with the U.S. federal government, three words will define your path forward: FedRAMP authorization. The Federal Risk and Authorization Management Program better known as FedRAMP is the government's standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services.
The federal government spends billions of dollars on cloud services each year, and every single vendor that wants a slice of that market must first prove their cloud offering meets a rigorous set of security standards. FedRAMP is the gatekeeper. It was established by the Office of Management and Budget (OMB) in 2011 to create a "do once, use many times" framework meaning a cloud provider achieves authorization once and can then be reused across federal agencies without each agency having to conduct its own independent security review.
In practice, the FedRAMP authorization process is one of the most demanding compliance journeys a company can undertake. It involves hundreds of security controls, third-party auditors, extensive documentation, and ongoing monitoring obligations. Without a clear roadmap, organizations often find themselves lost in a maze of requirements, wasting time and money on missteps that could have been avoided.
That's exactly why a well-structured FedRAMP authorization checklist is valuable and in this guide will walk you through everything, from what FedRAMP actually means, to the specific steps you need to take, to the real benefits waiting on the other side of authorization.
What Is FedRAMP Authorization?
FedRAMP authorization is the official process through which a cloud service provider (CSP) demonstrates that its cloud offering meets the federal government's security requirements and is approved for use by federal agencies. Think of it as a security certification specifically designed for cloud environments serving the U.S. government.
FedRAMP is built on top of the NIST Special Publication 800-53 security controls framework. These controls cover everything from access management and incident response to configuration management and system integrity. The FedRAMP program takes these NIST controls and tailors them specifically for cloud environments, adding requirements unique to multi-tenant, distributed systems.
When a CSP achieves FedRAMP authorization, it is granted an Authority to Operate (ATO) the formal federal approval to operate a cloud system within government environments. There are two primary pathways to this authorization. The first is a Joint Authorization Board (JAB) Provisional ATO, where a panel of Chief Information Officers from the Department of Defense, Department of Homeland Security, and the General Services Administration reviews and authorizes the cloud service for government-wide use. The second is an Agency ATO, where an individual federal agency sponsors the CSP and grants authorization for its own use which can then be leveraged by other agencies.
A critical concept in FedRAMP is the Cloud Service Offering (CSO), which refers to the specific product or service being authorized. This might be Infrastructure as a Service (IaaS), Platform as a Service (PaaS), or Software as a Service (SaaS). Each type carries its own considerations depending on what layers of the technology stack the CSP is responsible for securing.
FedRAMP authorization is a government-mandated stamp of approval that tells federal agencies: "This cloud service has been independently vetted, meets our security standards, and is safe to use."
Main FedRAMP Categories
FedRAMP organizes cloud services into three impact levels based on the potential consequences of a security breach. Understanding which category your cloud service falls into is the first major decision in the FedRAMP journey and it determines the number of security controls you'll need to implement.
FedRAMP Low applies to cloud systems where the loss of confidentiality, integrity, or availability would have a limited adverse effect on agency operations. These systems typically handle publicly available, non-sensitive information. FedRAMP Low requires approximately 125 security controls. While it's the least demanding of the three levels, "least demanding" is relative ; it still requires a comprehensive security assessment and formal authorization.
FedRAMP Moderate is by far the most common impact level, covering the vast majority of FedRAMP-authorized cloud services. It applies to systems where a security failure could cause serious adverse effects on operations, assets, or individuals. Controlled Unclassified Information (CUI) typically falls into this bucket. FedRAMP Moderate requires around 325 security controls and is the baseline most CSPs target when entering the federal market.
FedRAMP High is reserved for cloud systems handling the most sensitive government data information where a breach could cause severe or catastrophic damage. Think law enforcement data, emergency services systems, financial systems, and health information. FedRAMP High requires approximately 421 security controls and is the most rigorous authorization level. Very few CSPs currently hold FedRAMP High authorization, which makes achieving it a significant competitive differentiator.
Choosing the right impact level isn't just a technical decision, it's a strategic one. Underestimating your impact level can result in authorization rejection, while overestimating it can dramatically increase your costs and timeline unnecessarily.
Steps to Achieve FedRAMP Authorization
The FedRAMP authorization process is methodical and sequential. Skipping steps or rushing through them almost always creates problems down the line. Here is the complete FedRAMP authorization checklist broken down into actionable phases.
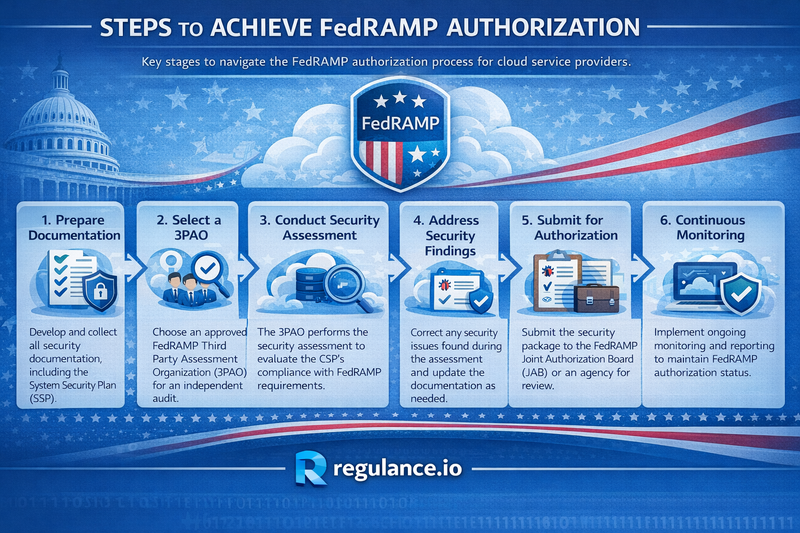
Step 1: Determine Your Readiness and Impact Level. Before anything else, conduct an internal gap assessment. Compare your current security posture against FedRAMP requirements for the impact level you're targeting. Identify where you meet requirements today and where significant work remains. This readiness assessment will inform your project timeline and resource requirements.
Step 2: Select Your Authorization Path. Decide whether you'll pursue a JAB Provisional ATO or an Agency ATO. The JAB path is more competitive and often longer but results in broader federal market access. The Agency path requires finding a federal agency willing to sponsor and collaborate on your authorization, a partnership that can significantly accelerate the process.
Step 3: Prepare Your System Security Plan (SSP). The SSP is the cornerstone document of FedRAMP authorization. It describes your system architecture, data flows, security controls in place, and how each FedRAMP control requirement is addressed. This document can run hundreds of pages and must be meticulously accurate. Any inconsistency between your SSP and your actual environment will be flagged during assessment.
Step 4: Achieve FedRAMP Ready Status (Optional but Recommended). The FedRAMP Marketplace allows CSPs to list as "FedRAMP Ready" after a Third Party Assessment Organization (3PAO) validates their readiness. While not mandatory, this designation signals to federal agencies that you're a serious contender and can attract sponsoring agencies.
Step 5: Engage a 3PAO for Independent Assessment. A FedRAMP-accredited 3PAO conducts an independent security assessment of your cloud system. They will test your controls, interview your staff, review your documentation, and produce a Security Assessment Report (SAR). Choose your 3PAO carefully their rigor and expertise directly impact how smoothly your authorization proceeds.
Step 6: Develop Your Plan of Action and Milestones (POA&M). The 3PAO's assessment will almost certainly surface findings vulnerabilities or gaps in your security posture. Your POA&M documents each finding and your plan to remediate it, including timelines and responsible parties. Federal reviewers will scrutinize your POA&M closely to ensure you're taking remediation seriously.
Step 7: Submit Your Authorization Package. Your complete authorization package including the SSP, SAR, POA&M, and supporting documentation is submitted to either the JAB or your sponsoring agency for review.
Step 8: Obtain Your ATO. After the reviewing body approves your package, you receive your Authority to Operate. You are now FedRAMP authorized. But the work doesn't stop here.
Step 9: Maintain Continuous Monitoring. FedRAMP requires ongoing monthly vulnerability scanning, annual security assessments, and immediate reporting of significant changes or incidents. Continuous monitoring is a permanent commitment, not an afterthought.
Benefits of Achieving FedRAMP Authorization
The FedRAMP authorization process is demanding, expensive, and time-consuming. So why do hundreds of cloud providers pursue it? Because the benefits are substantial and lasting.
Access to a massive federal market. The U.S. federal government is the world's largest consumer of cloud services. FedRAMP authorization unlocks access to contracts across dozens of agencies, from the Department of Defense to the Department of Veterans Affairs. Without authorization, this market is simply closed to you.
Competitive differentiation. FedRAMP authorization signals to all customers that your security posture has been independently validated against some of the world's most rigorous standards. Commercial customers increasingly use FedRAMP status as a proxy for security maturity when making procurement decisions.
Reduced sales friction. Once you're FedRAMP authorized, the "do once, use many times" principle means federal agencies can adopt your service without repeating the full security review. This dramatically shortens sales cycles with government customers and reduces the burden on both parties.
Strengthened internal security. The process of achieving FedRAMP authorization forces organizations to shore up security gaps, implement robust monitoring practices, and build a security-conscious culture. Many organizations emerge from the process with a genuinely stronger security program than they entered with.
Trust and credibility. Listing on the FedRAMP Marketplace as an authorized provider builds immediate credibility. Government contracting officers and procurement teams actively search the Marketplace when evaluating cloud vendors. Appearing there puts you in front of decision-makers who are actively looking to buy.
Frequently Asked Questions (FAQs)
How long does FedRAMP authorization take? The timeline varies widely. An Agency ATO can take anywhere from 6 months to over a year. The JAB path typically takes 12 to 18 months or more. Organizations that invest in readiness preparation upfront generally move through the process faster.
How much does FedRAMP authorization cost? Costs vary depending on your system's complexity and impact level. Most organizations spend between $500,000 and $2 million+ when accounting for 3PAO assessment fees, internal staff time, tooling, and documentation efforts. FedRAMP High assessments are significantly more expensive than Moderate.
What is a 3PAO and why do I need one? A Third Party Assessment Organization (3PAO) is an independent auditing firm accredited by the American Association for Laboratory Accreditation (A2LA) specifically for FedRAMP assessments. Federal regulations require that your security assessment be conducted by an accredited 3PAO to ensure objectivity and credibility.
Can I reuse my existing compliance certifications like SOC 2 or ISO 27001? While prior certifications demonstrate security maturity and can ease your preparation, they do not substitute for FedRAMP authorization. FedRAMP has its own specific control requirements, documentation standards, and assessment processes that must be independently satisfied.
What happens if my cloud environment changes after authorization? FedRAMP requires CSPs to report significant changes through a formal change management process. Major changes to your system architecture, data flows, or security controls may require a partial or full reassessment. This is part of why continuous monitoring is so important.
Is FedRAMP authorization permanent? No. FedRAMP authorization is maintained through continuous monitoring obligations including monthly vulnerability scans, annual penetration testing, and timely POA&M remediation. Failure to maintain these obligations can result in revocation of your ATO.
Don't let compliance complexity hold back your federal market ambitions. Visit Regulance today and take the first step toward regulatory compliance with a team that knows the process inside and out.