Third-Party Risk Management: Latest Statistics, Trends, and Best Practices for 2026


Introduction
Modern businesses don't operate in isolation anymore. From cloud service providers and payment processors to logistics partners and IT vendors, organizations today depend on an extensive network of external relationships to function efficiently. While these partnerships unlock growth opportunities and operational efficiencies, they also introduce a critical challenge that executives can no longer afford to ignore: third-party risk management.
Recent data shows that 61% of organizations have suffered data breaches originating from their vendors or third-party partners. These aren't isolated incidents affecting only large enterprises, businesses of all sizes face exposure through their extended ecosystem. When a vendor experiences a security incident, regulatory violation, or operational failure, the consequences ripple directly back to your organization, potentially damaging your reputation, finances, and customer trust.
What makes this particularly concerning is the scale of the problem. The average company now works with hundreds, sometimes thousands, of third parties, each representing a potential vulnerability. Yet despite this expanding attack surface, only 35% of organizations have implemented comprehensive third-party risk management programs. This gap between exposure and preparedness creates an environment where preventable incidents continue to disrupt businesses and erode stakeholder confidence.
Understanding the current landscape of third-party risks, backed by the latest statistics and research, is the first step toward building resilience. More importantly, knowing which proven strategies and best practices actually work can transform vendor relationships from potential liabilities into secure, value-driving partnerships that support long-term business success.
The Growing Third-Party Risk Landscape
According to recent industry research, 61% of organizations have experienced a data breach caused by a third party or vendor, highlighting the critical nature of this challenge. Even more concerning, 98% of organizations have relationships with at least one third party that has experienced a breach in the past two years. These statistics underscore a fundamental truth: your organization's security is only as strong as your weakest third-party link.
The average cost of a third-party data breach now exceeds $4.5 million, with some incidents resulting in losses surpassing tens of millions when factoring in regulatory fines, litigation costs, remediation expenses, and reputational damage. Beyond monetary losses, organizations face operational disruptions, customer trust erosion, and potential regulatory sanctions that can threaten long-term viability.
What is The Current State of Third-Party Risk Management?
Despite the clear and present danger, many organizations struggle with effective third-party risk management. Recent surveys indicate that 54% of companies say managing third-party risk is becoming more difficult, driven by factors including the increasing number of vendors, evolving regulatory requirements, and the sophisticated nature of modern cyber threats.
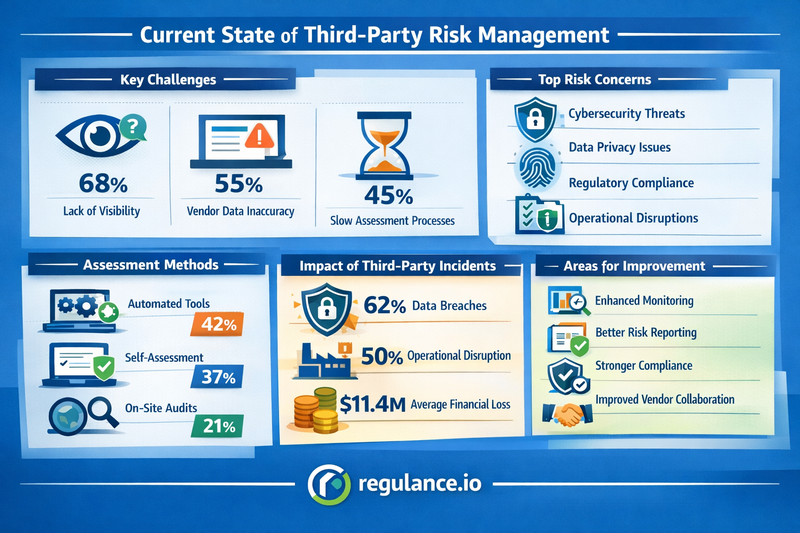
The challenge is compounded by the fact that 45% of organizations work with more than 1,000 third parties, while only 35% have a comprehensive third-party risk management program in place. This gap between exposure and preparedness creates significant vulnerability windows that threat actors are increasingly exploiting.
The shift toward digital transformation has accelerated third-party relationships, with cloud service providers, SaaS vendors, and managed service providers becoming integral to business operations. While these partnerships enable agility and innovation, they also expand the attack surface and create new risk dimensions that traditional security measures often fail to address.
Key Third-Party Risk Categories
Understanding the diverse nature of third-party risks is essential for developing comprehensive management strategies. These risks typically fall into several interconnected categories, each requiring specific attention and mitigation approaches.
Cybersecurity risks remain at the forefront of organizational concerns. When third parties gain access to your systems, networks, or data, they become potential entry points for cyberattacks. The 2021 SolarWinds breach, which compromised thousands of organizations through a trusted software vendor, demonstrated how a single compromised third party can cascade into a massive security incident affecting entire supply chains.
Compliance and regulatory risks have intensified as governments worldwide implement stricter data protection regulations. The GDPR, CCPA, HIPAA, and numerous other frameworks hold organizations accountable for their third parties' handling of sensitive information. Non-compliance can result in hefty fines, with GDPR penalties reaching up to 4% of global annual revenue.
Operational risks emerge when third-party failures disrupt critical business processes. Whether due to service outages, quality issues, or capacity constraints, operational dependencies on external providers can create single points of failure that impact your ability to serve customers and maintain business continuity.
Financial risks encompass everything from fraud and embezzlement to bankruptcy and insolvency of critical vendors. When a strategic supplier faces financial difficulties, it can trigger supply chain disruptions, price increases, or sudden service terminations that jeopardize your operations.
Reputational risks arise when third-party actions reflect poorly on your organization. Whether through data breaches, ethical violations, environmental incidents, or labor practices, the conduct of your vendors can directly impact public perception and stakeholder trust in your brand.
Latest Statistics of Third-Party Risk Management
Recent research provides valuable insights into the evolving third-party risk landscape. 73% of organizations report experiencing a third-party incident in the past year, ranging from minor security events to significant breaches requiring extensive remediation efforts.
The due diligence gap remains troubling. While 84% of organizations acknowledge the importance of vendor risk assessments, only 31% conduct thorough assessments of all their third parties. This selective approach leaves significant portions of the vendor ecosystem unmonitored and potentially vulnerable.
Technology adoption shows promise but remains inconsistent. 52% of organizations have invested in dedicated third-party risk management platforms, recognizing that spreadsheets and manual processes cannot scale to meet modern requirements. However, implementation challenges and resource constraints prevent many from maximizing these investments.
The concentration risk is real and growing. 68% of organizations rely on critical third parties for essential business functions, creating dependencies that, if disrupted, could threaten organizational survival. This concentration makes comprehensive risk management not just a security concern but a strategic business imperative.
Fourth-party risks, or risks stemming from your vendors' vendors, have emerged as a significant blind spot. Only 29% of organizations actively monitor fourth-party risks, despite evidence that these indirect relationships can pose substantial threats. The interconnected nature of modern supply chains means that vulnerabilities several steps removed can still impact your organization directly.
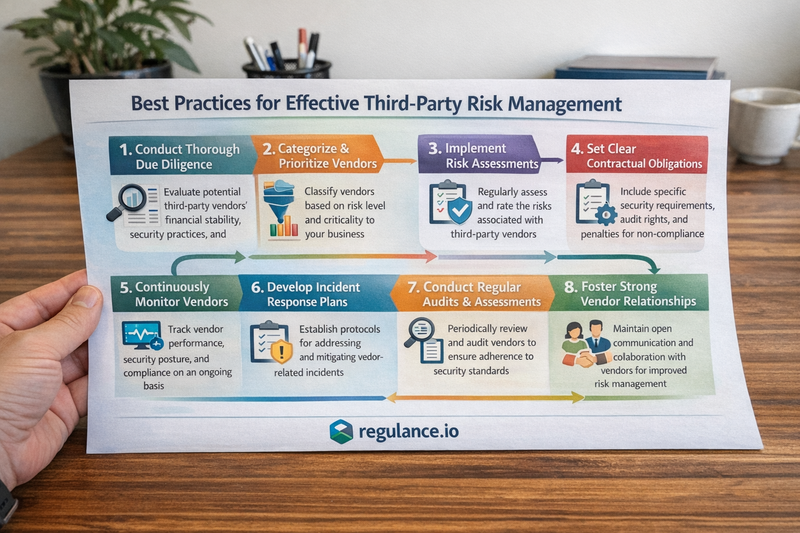
Best Practices for Effective Third-Party Risk Management
Building a robust third-party risk management program requires a systematic, comprehensive approach that addresses the entire vendor lifecycle from initial selection through ongoing monitoring and eventual offboarding.
Establish a comprehensive governance framework that defines roles, responsibilities, and accountability for third-party risk management across your organization. This framework should include clear policies, standardized procedures, and executive sponsorship to ensure adequate resources and organizational commitment. Designate a dedicated team or individual responsible for coordinating vendor risk activities and serving as the center of excellence for best practices.
Implement risk-based vendor classification to allocate resources efficiently. Not all third parties pose equal risk. Develop a tiering system that categorizes vendors based on factors including data access, criticality to operations, regulatory requirements, and inherent risk profiles. High-risk vendors warrant more intensive due diligence, frequent assessments, and continuous monitoring, while lower-risk relationships can follow streamlined processes.
Conduct thorough due diligence before engagement to understand potential risks before they materialize. Comprehensive vendor assessments should evaluate financial stability, security posture, compliance capabilities, business continuity plans, and reputation. Request evidence of certifications such as SOC 2, ISO 27001, or industry-specific standards relevant to your requirements. Don't rely solely on questionnaires; validate responses through independent research, reference checks, and when appropriate, on-site visits or audits.
Embed security and compliance requirements in contracts to create legal obligations and accountability mechanisms. Well-drafted vendor agreements should include specific security standards, data protection requirements, audit rights, incident notification obligations, liability provisions, and termination clauses. These contractual terms provide leverage for enforcing expectations and recovering damages if vendors fail to meet their obligations.
Implement continuous monitoring rather than relying solely on point-in-time assessments. The risk profile of third parties changes constantly due to new threats, business changes, mergers and acquisitions, or security incidents. Leverage automated tools that provide real-time threat intelligence, security ratings, and alerts about vendor-related risks. Supplement automation with periodic reassessments based on risk tier and regulatory requirements.
Develop incident response protocols that specifically address third-party breaches or failures. Your incident response plan should include procedures for notification requirements, containment strategies, investigation processes, communication plans, and recovery steps when third-party incidents occur. Conduct tabletop exercises that simulate vendor-related incidents to test and refine these procedures.
Foster collaborative relationships with strategic vendors around risk management. The most effective third-party risk management transcends adversarial compliance checking and builds partnerships where both parties work together to strengthen security and resilience. Share threat intelligence, conduct joint security reviews, and develop mutual improvement plans that benefit both organizations.
Invest in technology and automation to scale your program effectively. Modern third-party risk management platforms can streamline vendor assessments, centralize documentation, automate monitoring, generate risk dashboards, and facilitate collaboration across stakeholders. While technology doesn't replace human judgment, it dramatically improves efficiency and consistency.
Provide vendor security training to help third parties understand your requirements and best practices. Many smaller vendors lack sophisticated security programs and benefit from guidance. Offering training sessions, sharing resources, or providing access to security tools can strengthen the overall ecosystem while reducing your risk.
Monitor for concentration risks by ensuring that critical business functions aren't overly dependent on single vendors. Develop contingency plans, maintain backup vendors for critical services, and negotiate terms that facilitate transition if primary vendors fail. Geographic and technological diversification can also reduce concentration risks.
Address fourth-party risks by extending visibility beyond direct vendors. Require critical third parties to maintain their own vendor risk management programs and provide transparency into their high-risk subcontractors. Include flow-down provisions in contracts that extend your security requirements through the supply chain.
Measure and report program effectiveness through meaningful metrics and KPIs. Track indicators such as vendor assessment completion rates, time to complete due diligence, number of vendors by risk tier, incident frequency and severity, remediation timeframes, and compliance rates. Regular reporting to executives and boards demonstrates value and supports resource allocation decisions.
Emerging Trends Shaping the Future
The third-party risk management field continues to evolve rapidly in response to technological advances, regulatory changes, and threat landscape shifts. Several trends are reshaping how organizations approach vendor risk in 2026 and beyond.
Artificial intelligence and machine learning are revolutionizing risk assessment capabilities. Advanced algorithms can analyze vast amounts of structured and unstructured data to identify patterns, predict potential failures, and prioritize risks more accurately than traditional methods. These technologies enable more sophisticated continuous monitoring and early warning systems that detect subtle indicators of emerging vendor risks.
Regulatory pressure continues intensifying globally. New frameworks focusing specifically on third-party risk management, supply chain security, and operational resilience are emerging across industries and jurisdictions. Organizations must navigate an increasingly complex regulatory landscape that demands more rigorous vendor oversight, detailed documentation, and demonstrated accountability.
ESG considerations are becoming integral to third-party risk management. Stakeholders increasingly expect organizations to ensure their vendors meet environmental sustainability standards, maintain ethical labor practices, and demonstrate strong governance. Vendor selection and monitoring now routinely incorporate ESG criteria alongside traditional security and compliance factors.
The integration of third-party risk management with broader enterprise risk management frameworks is accelerating. Organizations recognize that vendor risks don't exist in isolation but intersect with strategic, operational, financial, and reputational risks across the enterprise. Holistic approaches that break down silos between risk domains provide more comprehensive protection.
Take Action With Regulance
Don't let third-party vulnerabilities become your organization's weakness. Contact Regulance today to discover how our third-party risk management solutions can transform your vendor oversight from a compliance burden into a strategic advantage.
Protect your organization, secure your reputation, and build resilience against the evolving threat landscape with a partner committed to your success.