How to Strengthen Security Using a Proven Vulnerability Scanning Process


Introduction
Cybersecurity threats evolve at an alarming pace and organizations face a constant barrage of potential attacks, from sophisticated ransomware to zero-day exploits that can compromise sensitive data and cripple operations within minutes. The stark reality is that most successful cyberattacks exploit known vulnerabilities that could have been identified and patched before attackers struck. This is where vulnerability scanning becomes not just important, but absolutely essential for any organization serious about protecting its digital infrastructure.
Vulnerability scanning is the foundational practice of proactively identifying security weaknesses in your systems, networks, and applications before malicious actors can exploit them. It is compared to comprehensive health check-up for your IT environment; one that reveals potential points of entry that hackers could use to breach your defenses. Yet despite its critical importance, many organizations either neglect regular vulnerability scanning or implement it ineffectively, leaving themselves exposed to preventable security incidents.
The consequences of inadequate vulnerability management are severe. Data breaches cost companies millions in remediation, regulatory fines, and reputational damage. Beyond financial losses, organizations face operational disruptions, loss of customer trust, and potential legal liability. However, with a well-structured vulnerability scanning process, businesses can dramatically reduce their attack surface and maintain a robust security posture. This comprehensive guide will walk you through everything you need to know about vulnerability scanning; from understanding the core concepts to implementing an effective scanning strategy that protects your organization from emerging threats.
What is the Vulnerability Scanning Process?
The vulnerability scanning process is a systematic, automated method of identifying, analyzing, and prioritizing security weaknesses within an organization's IT infrastructure. It involves using specialized software tools to probe systems, networks, applications, and devices for known vulnerabilities that could be exploited by attackers. These vulnerabilities might include outdated software versions, misconfigurations, missing security patches, weak passwords, or insecure default settings that create opportunities for unauthorized access.
Unlike penetration testing, which attempts to actively exploit vulnerabilities to assess their real-world impact, vulnerability scanning is a non-intrusive process that identifies and catalogs potential security gaps without causing damage or disruption. The scanning tools compare your systems against comprehensive databases of known vulnerabilities, such as the Common Vulnerabilities and Exposures (CVE) list, which contains thousands of documented security flaws across various software and hardware platforms. This comparison process allows organizations to quickly identify which known weaknesses exist in their environment.
The vulnerability scanning process generates detailed reports that assign severity ratings to each discovered vulnerability based on factors like exploitability, potential impact, and the existence of known exploits. These ratings, often using the Common Vulnerability Scoring System (CVSS), help security teams prioritize remediation efforts, focusing first on critical vulnerabilities that pose the greatest risk to the organization. Modern vulnerability scanners can assess a wide range of targets, including operating systems, web applications, databases, network devices, cloud infrastructure, and Internet of Things (IoT) devices. This comprehensive coverage ensures that no aspect of your digital infrastructure goes unexamined.
What makes vulnerability scanning particularly valuable is its ability to provide continuous visibility into an organization's security posture. As new vulnerabilities are discovered daily and systems constantly change through updates, deployments, and configuration modifications, regular scanning ensures security teams maintain an accurate, up-to-date understanding of their risk landscape. The window between vulnerability disclosure and active exploitation by attackers has narrowed dramatically, sometimes to just hours or days. By implementing a robust vulnerability scanning process, organizations can stay ahead of threat actors and address weaknesses before they become entry points for damaging cyberattacks.
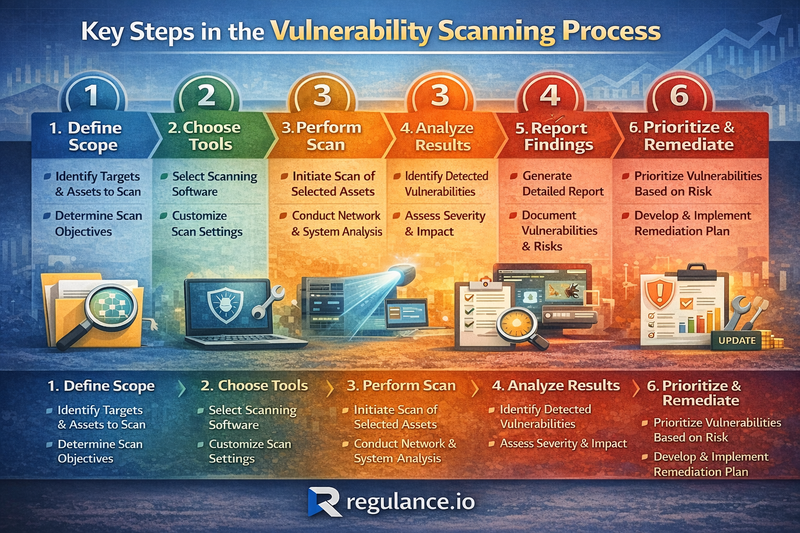
Key Steps in the Vulnerability Scanning Process
Implementing an effective vulnerability scanning process requires a structured approach. Here are the essential steps:
Asset Discovery and Inventory Before scanning for vulnerabilities, identify all devices, systems, applications, and network components within your infrastructure. A complete asset inventory should include servers, workstations, mobile devices, network equipment, and cloud resources.
Defining Scan Scope and Parameters Determine which systems will be included in each scan based on business criticality, data sensitivity, and compliance requirements. Configure scan timing to minimize operational disruption and select appropriate scan profiles.
Scanner Configuration and Optimization Proper configuration is crucial for accurate results. Set up scan policies defining which vulnerabilities to check, configure safe check options, establish scanning schedules, and integrate the scanner with other security tools.
Executing the Scan The vulnerability scanner probes systems using port scanning, banner grabbing, configuration analysis, and vulnerability signature matching. Modern scanners also perform web application scanning to identify issues like SQL injection vulnerabilities.
Results Analysis and Validation Review findings and validate genuine vulnerabilities through manual verification. Assess actual risk in context of your environment and filter false positives to focus on real threats.
Risk Prioritization Prioritize based on severity scores, exploitability, asset criticality, potential business impact, and available compensating controls.
Remediation Planning and Execution Develop a remediation roadmap that assigns vulnerabilities to appropriate teams, establishes realistic timelines, tracks progress, and implements temporary mitigations for vulnerabilities that cannot be immediately patched.
Verification and Rescanning After remediation, rescan affected systems to verify vulnerabilities have been properly addressed and no new issues were introduced.
Reporting and Documentation Maintain comprehensive records of scan results, remediation activities, and trends. Regular reporting demonstrates program value and supports informed decision-making.
Continuous Improvement Regularly review and refine your process based on lessons learned, emerging threats, infrastructure changes, and security incident feedback.
How Often Should You Perform Vulnerability Scanning?
Determining the right scanning frequency balances security effectiveness with operational considerations. There's no one-size-fits-all answer, the appropriate frequency depends on your specific circumstances.
Continuous or Daily Scanning High-security environments, critical infrastructure, and heavily regulated organizations benefit from continuous or daily scanning. This ensures new vulnerabilities are detected quickly, often within hours of system deployment. Financial institutions, healthcare organizations, and payment processors typically require this frequency.
Weekly Scanning Weekly scans strike a practical balance for many organizations, providing regular visibility without overwhelming security teams. This frequency allows teams to identify and address vulnerabilities before exploitation while maintaining manageable remediation workflows.
Monthly Scanning Less critical systems or stable environments might be adequately protected with monthly scans. This works well for internal systems with limited external exposure or legacy systems that change infrequently.
Event-Driven Scanning Certain events should trigger immediate assessments: deploying new systems, implementing major updates, discovering security incidents, making significant configuration changes, or receiving threat intelligence about emerging vulnerabilities.
Compliance Requirements Industry regulations mandate specific frequencies. PCI DSS requires quarterly scans plus scans after significant changes. HIPAA requires regular assessments. Defense contractors following NIST 800-171 must conduct periodic scans.
Most experts recommend a tiered approach with different frequencies based on asset criticality. Internet-facing systems should be scanned at least weekly. Critical internal infrastructure warrants weekly or bi-weekly scanning. Standard systems can be scanned monthly.
Things to Consider When Evaluating a Vulnerability Scanner
- Coverage and Detection Capabilities The scanner must identify vulnerabilities relevant to your environment, covering operating systems, network devices, applications, databases, and cloud infrastructure. Check database update frequency and emerging threat coverage.
- Accuracy and False Positive Rate Look for scanners with high accuracy and sophisticated validation mechanisms that reduce false positives. Request vendor testing methodology information and conduct proof-of-concept scans.
- Scan Speed and Performance Impact Scanning shouldn't significantly degrade network performance or disrupt operations. Evaluate speed, efficiency, and the ability to throttle scan intensity.
- Credentialed vs. Non-Credentialed Scanning Verify support for both credentialed scans (deeper visibility) and non-credentialed scanning modes, allowing appropriate approach selection based on security policies.
- Risk Prioritization and Scoring Look for intelligent prioritization beyond simple CVSS scores. The best scanners consider threat intelligence, asset criticality, exploitability, and environmental context.
- Integration Capabilities Your scanner should integrate with SIEM platforms, ticketing systems, configuration management tools, and threat intelligence feeds. Strong API support enables automation.
- Compliance and Reporting Features Ensure the scanner provides pre-built compliance reports for relevant standards like PCI DSS, HIPAA, or NIST. Reporting should allow customization for different audiences.
- Scalability and Deployment Options Evaluate cloud-based SaaS solutions, on-premises appliances, and distributed scanning architectures. Ensure the licensing model aligns with your organization's size.
- Ease of Use and User Experience An intuitive interface reduces training requirements. Look for clear dashboards, streamlined workflows, contextual help, and role-based access controls.
- Remediation Guidance and Workflow Support The scanner should provide actionable remediation guidance, including specific fix steps, links to patches, and automated remediation capabilities where possible.
- Vendor Support and Community Evaluate vendor reputation, financial stability, and product development commitment. Consider technical support quality, training resources, and user community strength.
FAQs
What's the difference between vulnerability scanning and penetration testing?
Vulnerability scanning is automated and identifies potential weaknesses by comparing systems against known vulnerability databases. Penetration testing involves experts actively attempting to exploit vulnerabilities to assess real-world impact. Both are valuable, scanning provides broader coverage while penetration testing offers deeper insights.
Can vulnerability scanning disrupt business operations?
Modern scanners minimize operational impact, but disruption is possible with aggressive configurations. Properly configure scanners, schedule scans during maintenance windows for critical systems, and use safe-check options to avoid disruptive tests.
Do I need different scanners for different assets?
While comprehensive scanners assess multiple asset types, specialized scanners often provide better results for specific technologies. Many organizations use general-purpose scanners for broad coverage and specialized tools for critical applications.
How do I prioritize which vulnerabilities to fix first?
Consider vulnerabilities with known exploits, those affecting internet-facing systems, existence on systems with sensitive data, high CVSS scores combined with exploitability, compliance requirements, and available patches or workarounds.
What should I do if I can't immediately fix a critical vulnerability?
Implement compensating controls like network segmentation, additional monitoring, web application firewalls, access restrictions, or disabling vulnerable services. Document mitigations and establish permanent remediation timelines.
Should vulnerability scanning be outsourced or handled internally?
This depends on resources, expertise, and requirements. Internal scanning provides control and faster response. Outsourced scanning offers specialized expertise and third-party validation. Many organizations use a hybrid approach.
Conclusion
Vulnerability scanning is a fundamental requirement for any organization serious about protecting digital assets and maintaining stakeholder trust. An effective process involves careful planning, proper tool selection, consistent execution, and systematic remediation based on findings.
Successful organizations scan frequently, prioritize based on actual risk, integrate scanning into broader security workflows, maintain complete asset visibility, and continuously refine their processes based on performance metrics. They understand vulnerability scanning isn't a point-in-time activity but an ongoing practice that must evolve alongside infrastructure and emerging threats.
Perfect security is impossible, new vulnerabilities emerge daily and attackers constantly develop new exploitation techniques. However, implementing robust vulnerability scanning dramatically reduces your attack surface and ensures known weaknesses are addressed before becoming breach points. The key is starting where you are, implementing consistent practices, and progressively improving your program over time.
Don't wait for a security incident to prioritize vulnerability management. Vulnerabilities exist in your environment right now, and attackers are actively scanning for them every single day.
Take Action with Regulance
Ready to strengthen your vulnerability management program? Contact Regulance today for a consultation and discover how our expertise can help you build a vulnerability management program that protects your digital assets, satisfies compliance requirements, and gives you confidence in your security posture.