How Did the Biggest Data Breaches of 2025 Happen and What Can Your Cybersecurity Team Do Better?


Introduction
The digital space of 2025 has proven to be one of the most challenging years for cybersecurity on record. As organizations increasingly depend on digital infrastructure, cybercriminals have responded with unprecedented sophistication and scale. This year witnessed massive data breaches affecting billions of individuals worldwide, from students to healthcare patients, from banking customers to insurance policyholders.
The year brought several alarming trends: third-party vendor compromises emerged as the primary attack vector, credential theft continued to dominate breach techniques, and the healthcare sector remained the most expensive target for attacks. With over 4,100 publicly disclosed data breaches occurring last year alone, the message is clear; no organization is immune to cyber threats. The average cost of a data breach now stands at $4.44 million, with companies taking an average of 241 days to identify and contain incidents.
Understanding these breaches is very important especially if you are handling massive amounts of data. Every data breach represents lessons learned, vulnerabilities exposed, and opportunities to strengthen cybersecurity defenses. This article examines the top 10 data breaches of 2025, exploring how they occurred, their impact on compliance frameworks, and most importantly, how your business can protect itself moving forward into 2026.
What is a Data Breach?
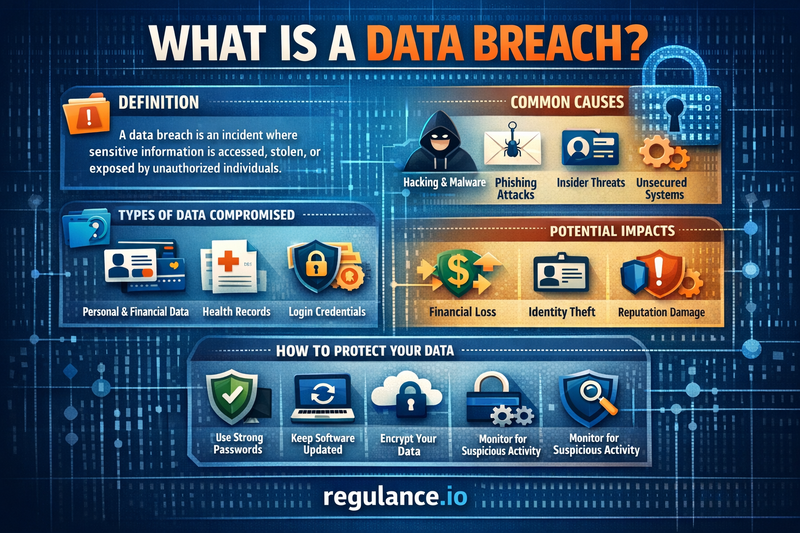
A data breach occurs when unauthorized individuals gain access to confidential, sensitive, or protected information. This can include personally identifiable information (PII) such as names, addresses, Social Security numbers, financial records, medical histories, login credentials, and proprietary business data. Data breaches represent serious security incidents that can result from various causes including cyberattacks, human error, system vulnerabilities, or inadequate security measures.
Types of Data Breach Incidents
Traditional Data Breaches: These involve unauthorized infiltration of secure systems through hacking, malware, or exploiting security vulnerabilities. Attackers typically target databases, servers, or networks to extract valuable information.
Data Leaks: Unlike breaches involving active intrusion, data leaks occur when information is inadvertently exposed due to misconfiguration, poor security practices, or unsecured databases. These incidents often involve information being left publicly accessible without password protection.
Insider Threats: Not all data breaches originate from external actors. Insider threats involve employees, contractors, or other authorized individuals who misuse their access privileges to steal or expose sensitive data, either maliciously or accidentally.
Common Attack Vectors
Modern data breaches typically exploit several key vulnerabilities. Credential theft remains the leading attack method, with over 74% of breaches involving human elements such as stolen passwords or social engineering. Phishing attacks trick employees into revealing login information or clicking malicious links. Third-party vendor compromises have become increasingly common, as attackers recognize that targeting a single supplier can provide access to dozens of organizations. Additionally, unpatched systems, misconfigured cloud services, and inadequate access controls continue to create opportunities for cybercriminals.
Understanding these fundamental concepts is essential for recognizing that data breaches are not random occurrences. They result from specific vulnerabilities that, when understood and addressed, can significantly reduce organizational risk.
Top 10 Data Breaches of 2025
1. PowerSchool Student Information System Breach – 62 Million Records
What Happened: In December 2024, discovered in January 2025, the PowerSchool breach became one of the largest education-sector incidents in history. An attacker used a compromised contractor credential to access the PowerSource customer support portal, which lacked multi-factor authentication at the time. This single entry point provided access to PowerSchool's Student Information System, affecting approximately 62 million students and nearly 10 million educators across North America.
Data Compromised: The breach exposed names, dates of birth, contact information, Social Security numbers, medical alert information, and in some cases, historical data spanning up to 40 years. The Toronto District School Board alone saw data from nearly 1.5 million students compromised.
Impact: PowerSchool paid approximately $2.85 million in ransom to prevent data release, though extortion attempts continued months later. Multiple lawsuits followed, including a significant action filed by the Texas Attorney General. The incident highlighted critical vulnerabilities in education technology infrastructure and raised serious questions about third-party vendor security practices. A 19-year-old Massachusetts student, Matthew D. Lane, later pleaded guilty to charges related to the attack and faced over nine years in prison.
2. Credentials Compilation Leak – 16 Billion Login Credentials
What Happened: June 2025 witnessed potentially the largest credential exposure in history when researchers discovered a massive database containing approximately 16 billion usernames and passwords. This wasn't a single breach but rather an aggregation of credentials collected from infostealer malware, phishing campaigns, and multiple prior data breaches.
Data Compromised: The database included login credentials for major platforms including Google, Apple, Meta (Facebook), and countless other services. The compilation revealed the devastating impact of password reuse across multiple accounts.
Impact: While no single company suffered a direct breach, the leak enabled widespread credential stuffing attacks where cybercriminals could automatically test stolen passwords across numerous services. Security firms issued urgent warnings for password resets and multi-factor authentication implementation. The incident demonstrated a systemic vulnerability affecting billions of users worldwide and highlighted the critical importance of unique, strong passwords for every account.
3. AT&T Customer Data Exposure – 86 Million Records
What Happened: In May 2025, AT&T found itself in the headlines again when a dataset containing personal details of over 86 million customers appeared for sale on the dark web. While AT&T indicated the data may have originated from older breaches, customers discovered their information circulating online in newly compiled formats.
Data Compromised: The exposed information included full names, addresses, dates of birth, email addresses, and critically, at least 44 million Social Security numbers. This combination of data created significant identity theft risks for affected individuals.
Impact: Multiple class-action lawsuits were filed, and regulators opened fresh investigations into AT&T's security practices. The incident underscored a troubling reality: once data escapes organizational control, it can remain in circulation indefinitely, becoming more dangerous when combined with other stolen information. The breach highlighted the long-term consequences of inadequate data protection.
4. Qantas Airways Customer Records – 6 Million Records
What Happened: In June 2025, Australian airline Qantas suffered a ransomware attack orchestrated by the Scattered Lapsus$ Hunters group. Cybercriminals exploited vulnerabilities in a third-party system integrated with Salesforce. When Qantas refused to pay the ransom, the attackers released customer data on the dark web.
Data Compromised: Nearly 6 million customer records were exfiltrated, including names, email addresses, phone numbers, physical addresses, and frequent-flyer account details. Importantly, no financial records appeared in the leaked data.
Impact: The breach forced Qantas to strengthen its security measures significantly and highlighted the risks associated with third-party integrations. The incident contributed to growing concerns about Salesforce-connected systems, as multiple 2025 breaches shared similar attack patterns involving compromised third-party applications with Salesforce access.
5. TransUnion Credit Data Breach – 4.4 Million Customers
What Happened: July 2025 brought serious concern when TransUnion, one of the major credit reporting agencies, experienced a significant breach. Attackers exploited misconfigured API permissions within a third-party integration connected to Salesforce, enabling large-scale data exfiltration without triggering standard access controls.
Data Compromised: The breach exposed highly sensitive information including Social Security numbers, credit-related data, and personal details of more than 4.4 million customers. The ShinyHunters threat actor group was believed responsible for the attack.
Impact: As TransUnion services over 100 million U.S. customers and more than 1 billion globally, the breach raised alarm about the security of financial data infrastructure. The incident demonstrated how API misconfigurations in third-party integrations could bypass multiple security layers, exposing the most sensitive consumer financial information.
6. SK Telecom Subscriber Data – 27 Million Records
What Happened: In April 2025, South Korea's largest telecommunications provider reported a catastrophic breach exposing data for nearly 27 million subscribers. Subsequent regulatory investigations revealed that SK Telecom's internal systems lacked fundamental security safeguards including unpatched servers, weak passwords, poor logging capabilities, and delayed detection mechanisms.
Data Compromised: The breach included subscriber identity module (USIM) data, personal information, and account details. This type of data potentially enabled SIM-swap attacks, where criminals could hijack phone numbers to bypass two-factor authentication or intercept sensitive communications.
Impact: South Korea's Ministry of Science and ICT imposed a historic fine equivalent to $96 million, one of the largest penalties ever levied for a data breach in the country. The ministry also ordered comprehensive security upgrades across SK Telecom's infrastructure. The incident served as a stark reminder that even major telecommunications providers in technologically advanced nations remain vulnerable without proper security fundamentals.
7. Yale New Haven Health System – 5.5 Million Patient Records
What Happened: The Yale New Haven Health (YNHHS) breach in March 2025 affected over 5.5 million individuals, making it one of the year's largest healthcare data incidents. The breach traced back to a third-party file transfer service vulnerability that allowed unauthorized access to protected health information stored within the organization's systems.
Data Compromised: Exposed data included medical record numbers, treatment information, Social Security numbers, insurance details, and other protected health information (PHI). This comprehensive dataset represented years of patient medical histories.
Impact: A class-action lawsuit filed in April led to an $18 million settlement over allegations of inadequate cybersecurity controls. Healthcare remains the costliest sector for data breaches, with long-lived medical records and operational pressure creating unique vulnerabilities. The incident highlighted critical weaknesses in third-party file transfer services and the healthcare industry's ongoing struggle to balance accessibility with security.
8. Blue Shield of California Analytics Misconfiguration – 4.7 Million Customers
What Happened: Blue Shield of California experienced a data breach resulting from a Google Analytics misconfiguration on certain company websites. This type of breach demonstrates how seemingly minor technical oversights can expose massive amounts of customer data.
Data Compromised: The misconfiguration inadvertently exposed data for approximately 4.7 million customers, including protected health information such as insurance details, demographic information, service dates, provider information, patient names, financial responsibility records, and search activity on the company's websites.
Impact: The incident illustrated the hidden risks of analytics and tracking tools. Many organizations fail to properly configure third-party analytics platforms, unknowingly transmitting sensitive data to external servers. The breach prompted renewed scrutiny of how healthcare providers implement website tracking technologies and underscored the importance of privacy-by-design principles.
9. Orange Romania Telecommunications – 3.4 Million Records
What Happened: In February 2025, a hacker identified as "Rey" obtained more than 3.4 million records from Orange's Romanian branch following a ransomware attack. Orange declined to pay the ransom, resulting in the stolen data appearing on the dark web.
Data Compromised: Customer information including names, dates of birth, addresses, phone numbers, email addresses, usernames, and ID numbers was compromised. This combination provided cybercriminals with sufficient information to conduct identity theft, targeted phishing campaigns, and social engineering attacks.
Impact: Orange coordinated with Romania's National Cybersecurity Directorate (DNSC) to monitor the situation and assess the full scope of the breach. The incident added to growing concerns about telecommunications infrastructure security across Europe and demonstrated the difficult position companies face when deciding whether to negotiate with ransomware attackers.
10. U.S. Treasury Contractor System Breach
What Happened: In late December 2024, continuing into 2025, the U.S. Treasury learned that cybercriminals had compromised a contractor's remote support tool. These remote access tools allow vendors to access systems as if physically present in the office. Attackers exploited this trusted access to reach unclassified Treasury computers and documents. Investigations pointed to a threat group linked to China.
Data Compromised: While the full extent remains under investigation, the breach involved access to unclassified Treasury documents and systems. The compromise demonstrated how third-party remote access tools could serve as backdoors into sensitive government networks.
Impact: The incident raised serious national security concerns and prompted comprehensive reviews of contractor access protocols across federal agencies. It highlighted the critical importance of securing remote access tools and maintaining strict oversight of third-party vendor permissions, particularly for government entities handling sensitive information.
Impact on Compliance from the Most Recent Data Breaches
The 2025 data breaches have sent shockwaves through compliance departments worldwide, forcing organizations to confront the real-world consequences of regulatory non-compliance. These incidents have accelerated enforcement actions and fundamentally reshaped how businesses approach data protection requirements.
Escalating Financial Penalties
Regulatory bodies demonstrated unprecedented willingness to impose substantial penalties in 2025. Under the General Data Protection Regulation (GDPR), companies face fines of up to €20 million or 4% of global annual revenue, whichever is higher. The trend continued in 2025, with over 80% of GDPR fines issued for insufficient security measures leading to data leaks. Meta's record €1.2 billion fine from 2023 established a precedent that regulators would not hesitate to levy maximum penalties for serious violations.
In the United States, the California Consumer Privacy Act (CCPA) enforcement reached historic levels. The California Privacy Protection Agency announced a record $1.35 million settlement with Tractor Supply Company in September 2025, signaling aggressive state-level enforcement. CCPA violations can cost businesses up to $7,500 per incident for intentional violations, with no cap on total penalties. When multiplied across thousands or millions of affected consumers, penalties quickly reach devastating levels.
Mandatory Breach Notification Requirements
The 2025 breaches highlighted the critical importance of timely breach notifications. GDPR requires organizations to notify supervisory authorities within 72 hours of discovering a breach, while also informing affected individuals if there's high risk to their rights. Many 2025 incidents revealed significant delays between breach discovery and notification, resulting in additional penalties beyond those for the security failures themselves.
PowerSchool's delayed notification, waiting weeks before informing all affected parties—drew particular scrutiny from privacy commissioners. Canadian and American regulators criticized both PowerSchool and the school boards for inadequate breach response planning. The investigations emphasized that notification delays compound the harm to individuals and demonstrate organizational failure to prioritize data subject rights.
Third-Party Vendor Accountability
Perhaps the most significant compliance shift involves third-party vendor management. The 2025 breaches demonstrated that organizations cannot simply outsource responsibility for data protection. Under GDPR Article 28, data controllers must ensure that processors provide sufficient guarantees of GDPR compliance. Contracts must include specific data protection clauses, and controllers bear responsibility for choosing processors carefully.
The PowerSchool incident proved particularly instructive. Privacy commissioners found that many school boards lacked basic contractual safeguards, proper monitoring of security measures, and enforcement mechanisms in vendor agreements. Organizations learned that compliance requires active oversight, not just signed contracts gathering dust in filing cabinets.
Industry-Specific Compliance Challenges
Healthcare organizations faced intensified scrutiny following the Yale New Haven Health and Blue Shield of California breaches. The Health Insurance Portability and Accountability Act (HIPAA) requires administrative, physical, and technical safeguards for protected health information. The $18 million Yale settlement established that courts and regulators expect healthcare organizations to maintain cybersecurity measures proportionate to the sensitivity of medical data.
Financial services encountered similar pressure. TransUnion's breach triggered multiple investigations examining compliance with the Gramm-Leach-Bliley Act (GLBA), which mandates financial institutions to protect customer information. With credit reporting agencies holding exceptionally sensitive data, regulators demonstrated they would hold these institutions to the highest security standards.
Data Minimization and Retention Policies
Multiple 2025 breaches exposed decades of unnecessary data retention. The PowerSchool incident revealed that some school districts maintained 40 years of student records without clear retention policies or data minimization practices. Privacy regulations increasingly emphasize storing only necessary data and implementing clear deletion schedules. Organizations maintaining excessive historical data face not only increased breach exposure but also regulatory criticism for failing to implement data minimization principles.
Enhanced Security Requirements
The breaches accelerated regulatory emphasis on specific security measures. Multi-factor authentication (MFA) became a de facto compliance requirement after PowerSchool's lack of MFA on critical systems contributed to the breach. Regulators made clear that certain baseline security measures are no longer optional; they represent minimum acceptable standards.
Encryption requirements also intensified. While GDPR doesn't mandate specific encryption standards, it explicitly mentions encryption as a recommended safeguard. Organizations experiencing breaches of unencrypted data faced harsher penalties and criticism compared to those where encryption limited the impact.
The Compliance Shift for 2026
Looking ahead, organizations can expect compliance frameworks to become more prescriptive rather than principle-based. The new CCPA regulations taking effect January 1, 2026, introduce mandatory risk assessments, enhanced rules around cookies and pixels, and new data broker requirements. The EU's Digital Omnibus proposals aim to streamline but also strengthen requirements around incident reporting under NIS2, GDPR, and the Cyber Resilience Act.
Compliance in 2026 will require proactive rather than reactive approaches. Organizations must implement continuous monitoring, regular audits, comprehensive vendor management programs, and incident response capabilities tested through regular drills. The message from 2025's breaches is unmistakable: compliance represents not just regulatory obligation but fundamental business survival in an increasingly hostile threat landscape.
How to Protect Your Business in 2026
The data breaches of 2025 provide critical lessons for building stronger defenses in 2026. Protection requires layered security approaches combining technology, policies, and human awareness. Here are comprehensive strategies to safeguard your organization.
Implement Zero Trust Architecture
Zero Trust represents a fundamental shift from traditional security models. Instead of assuming everything inside your network is safe, Zero Trust requires continuous verification of every user, device, and application attempting to access resources. This approach proved its value in 2025, as breaches involving lateral movement, where attackers moved freely after initial compromise caused the most damage.
Implement Zero Trust by requiring authentication for all access attempts, limiting permissions to the minimum necessary (principle of least privilege), and segmenting networks to contain potential breaches. Deploy micro-segmentation to create security zones within your network, preventing attackers from moving laterally if they breach one area.
Mandate Multi-Factor Authentication Everywhere
The PowerSchool breach demonstrated the devastating consequences of missing MFA on critical systems. Multi-factor authentication should be mandatory for all systems containing sensitive data, administrative functions, remote access, cloud services, and email accounts.
Choose strong MFA methods. While SMS-based codes provide better security than passwords alone, they remain vulnerable to SIM-swapping attacks like those enabled by the SK Telecom breach. Prefer authenticator apps, hardware security keys, or biometric authentication for high-value systems. For executive accounts and administrators, require phishing-resistant MFA such as FIDO2 security keys.
Strengthen Vendor and Third-Party Management
Third-party compromises dominated 2025's breach landscape. Organizations must recognize that vendor security directly impacts their own risk profile. Implement comprehensive vendor management programs including rigorous security assessments before onboarding, contractual requirements for specific security standards, annual security audits and questionnaires, incident notification clauses requiring immediate disclosure, and right-to-audit provisions allowing verification of security claims.
Minimize vendor access to only what's necessary and implement separate authentication for each vendor, never share credentials. Monitor vendor access logs for unusual activity and establish processes for immediately revoking access when relationships end.
Deploy Comprehensive Encryption
Encryption transforms data breaches from catastrophes into manageable incidents. Implement encryption for data at rest (stored information on servers, databases, and backups), data in transit (information moving across networks), and end-to-end encryption for particularly sensitive communications.
Organizations implementing enterprise encryption strategies experienced 70% reduced impacts from data breaches compared to those without comprehensive encryption coverage. While encryption doesn't prevent breaches, it renders stolen data far less valuable to attackers and, under regulations like GDPR, can eliminate breach notification requirements if encrypted data is stolen.
Establish Robust Data Governance
Many 2025 breaches exposed unnecessary data retention spanning decades. Implement data governance frameworks including comprehensive data inventories identifying all information you collect and store, classification systems categorizing data by sensitivity level, retention policies specifying how long each data type should be kept, and automated deletion processes removing data when retention periods expire.
Apply data minimization principles by collecting only information you genuinely need and regularly purging unnecessary historical data. Remember: data you don't retain cannot be stolen in a breach.
Continuous Employee Training and Awareness
Human error contributed to 74% of breaches in 2025. Regular cybersecurity training is essential, but traditional annual compliance courses prove ineffective. Implement continuous security awareness programs with quarterly training sessions on current threats, monthly simulated phishing exercises testing real-world readiness, immediate micro-learning when employees fail phishing tests, and clear reporting procedures for suspicious activity.
Create a security-conscious culture where employees feel comfortable reporting mistakes or potential compromises without fear of punishment. Early reporting can mean the difference between a contained incident and a catastrophic breach.
Deploy Advanced Threat Detection
Traditional perimeter defenses proved insufficient in 2025. Organizations must detect threats that breach initial defenses through endpoint detection and response (EDR) solutions monitoring individual devices, security information and event management (SIEM) platforms aggregating and analyzing security logs, managed detection and response (MDR) services providing 24/7 monitoring with expert analysts, and user and entity behavior analytics (UEBA) identifying anomalous activities suggesting compromise.
Continuous monitoring enables organizations to detect breaches in hours rather than the 241-day average identification time. Speed of detection dramatically reduces breach impact and costs.
Implement Least Privilege Access Controls
Excessive permissions enabled many 2025 breaches to escalate quickly. Implement least privilege principles by granting users and applications only the minimum access necessary for their functions, reviewing and adjusting permissions quarterly, implementing just-in-time access providing elevated privileges only when needed and immediately revoking them, separating duties so no single person has complete control over critical processes, and automatically deprovisioning access when employees change roles or leave.
The principle is simple: if an account doesn't need access to certain data or systems, it shouldn't have it. This dramatically limits damage from compromised credentials.
Secure Cloud Configurations
Misconfigurations caused multiple 2025 breaches, including Blue Shield's Google Analytics incident. As organizations increasingly rely on cloud services, proper configuration becomes critical. Implement cloud security posture management (CSPM) tools to continuously scan for misconfigurations, enforce security baselines across all cloud resources, regularly review access permissions and public exposure settings, enable cloud provider security features and logging, and implement infrastructure-as-code to ensure consistent secure configurations.
Never assume cloud services are secure by default. Security in the cloud remains the customer's responsibility.
Establish and Test Incident Response Plans
Every organization will eventually face a security incident. The difference between contained incidents and catastrophic breaches often lies in response preparation. Develop comprehensive incident response plans including clear roles and responsibilities, communication protocols for internal and external stakeholders, technical procedures for containment and recovery, legal and regulatory notification requirements, and vendor contact information for immediate assistance.
Test these plans through regular tabletop exercises and simulations. Organizations that practiced responses handled 2025's actual incidents far more effectively than those developing plans on the fly during crises.
Regular Security Assessments and Penetration Testing
You cannot protect what you don't understand. Regular security assessments identify vulnerabilities before attackers exploit them. Conduct quarterly vulnerability scans, annual penetration testing by qualified professionals, security architecture reviews when implementing new systems, and continuous risk assessments considering evolving threats.
Third-party security audits provide valuable external perspectives and help identify blind spots internal teams might miss.
Invest in Backup and Recovery Capabilities
While prevention remains the goal, organizations must prepare for potential compromises. Implement robust backup strategies with regular automated backups stored both onsite and in secure cloud locations, offline backups disconnected from networks to prevent ransomware encryption, regular testing of restoration procedures to ensure backups actually work, and clear recovery time objectives (RTO) and recovery point objectives (RPO) based on business needs.
The difference between ransomware being an expensive inconvenience versus an existential threat often comes down to backup quality and restoration capabilities.
Stay Current with Security Updates
Unpatched systems represent easy targets for attackers. Implement patch management programs ensuring operating systems, applications, firmware, and security tools receive timely updates. Prioritize critical security patches and deploy them within days rather than weeks. Consider automated patch management tools for consistent, rapid deployment across your environment.
Frequently Asked Questions (FAQs)
Q: What should I do if my organization experiences a data breach?
A: Immediately activate your incident response plan. Contain the breach by isolating affected systems, preserve evidence for investigation, engage your legal team and cybersecurity professionals, determine notification obligations under relevant regulations (typically within 72 hours for GDPR), notify affected individuals as required, and document every step for regulatory and legal purposes. Speed matters, both for limiting damage and meeting legal requirements.
Q: How long does a company have to notify individuals about a data breach?
A: Notification timeframes vary by jurisdiction. GDPR requires notifying supervisory authorities within 72 hours of breach discovery and affected individuals "without undue delay" if there's high risk to their rights. Most U.S. state breach notification laws require notification within 30-60 days. California's CCPA requires notification "in the most expedient time possible." Always consult legal counsel as requirements differ based on data types, jurisdiction, and circumstances.
Q: Are small businesses required to comply with data protection regulations?
A: Yes, though thresholds vary. GDPR applies regardless of organization size if you process EU residents' data. CCPA applies to businesses with $25 million+ annual revenue, buying/selling data of 100,000+ California residents, or deriving 50%+ revenue from selling personal information. Many other state privacy laws include similar thresholds. Even if not legally required, implementing strong data protection builds customer trust and reduces breach risk.
Q: What's the difference between a data breach and a data leak?
A: Data breaches involve unauthorized access through active intrusion hacking, malware, or exploiting vulnerabilities. Data leaks occur when information is inadvertently exposed through misconfiguration, poor security practices, or unsecured systems. Leaks often involve data left publicly accessible without password protection. Both result in unauthorized data exposure but differ in attack method.
Q: How much does the average data breach cost?
A: According to IBM's 2025 Cost of Data Breach Report, the average breach costs $4.44 million. However, costs vary significantly based on industry, breach size, and data sensitivity. Healthcare breaches cost the most, averaging over $10 million. Costs include investigation, remediation, notification, legal fees, regulatory fines, business disruption, and long-term reputation damage. Organizations with strong security measures experience significantly lower breach costs.
Q: Can cyber insurance protect against data breach costs?
A: Cyber insurance can cover many breach-related expenses including forensic investigation, legal fees, notification costs, credit monitoring for affected individuals, public relations expenses, and some regulatory fines (depending on jurisdiction). However, insurance doesn't cover everything, particularly punitive damages or fines resulting from gross negligence. Importantly, insurers increasingly require strong security measures before issuing policies.
Q: What is the most common cause of data breaches?
A: Stolen or compromised credentials remain the leading attack vector, involved in over 74% of breaches according to Verizon's 2025 Data Breach Investigations Report. This includes phishing attacks tricking employees into revealing passwords, credential stuffing using passwords stolen in previous breaches, brute force attacks guessing weak passwords, and session hijacking. The human element whether through social engineering, poor password practices, or inadequate security awareness underlies most successful attacks.
Q: How can I tell if my personal information was part of a data breach?
A: Monitor several sources: check breach notification websites like HaveIBeenPwned.com which aggregates breach data, watch for official notifications from companies you do business with (required by law), monitor credit reports for suspicious activity, review bank and credit card statements regularly, and enable dark web monitoring services offered by some identity protection providers. If you discover your information in a breach, immediately change passwords for affected accounts, enable multi-factor authentication, and consider placing fraud alerts or credit freezes.
Q: What's the best way to create strong passwords?
A: Use unique, complex passwords for every account never reuse passwords. Strong passwords include 12+ characters combining uppercase, lowercase, numbers, and symbols. Consider using passphrases (random words strung together) which provide both security and memorability. However, the best approach is using a password manager to generate and store truly random passwords. Password managers eliminate the need to remember dozens of complex passwords while ensuring each account has unique, strong credentials protecting you if one service experiences a breach.
Q: How often should we conduct security training for employees?
A: Quarterly formal training sessions with monthly phishing simulations provide effective ongoing awareness. However, security awareness shouldn't be confined to scheduled training. Implement continuous micro-learning with brief, timely lessons when relevant events occur. Send regular security tips and updates. Create a culture where security remains top-of-mind rather than something addressed only during annual compliance sessions. Research shows continuous reinforcement proves far more effective than annual training alone.
Conclusion
The data breaches of 2025 serve as stark reminders that cybersecurity threats continue evolving in sophistication and scale. From PowerSchool's compromise affecting millions of students to the massive 16 billion credential compilation, these incidents demonstrate that no sector remains immune from cyber threats. Third-party vulnerabilities, credential theft, and inadequate security fundamentals enabled most major breaches, highlighting areas where organizations must strengthen defenses.
The compliance landscape has responded with increased enforcement, substantial penalties, and heightened expectations for security measures. Regulators worldwide demonstrated unwillingness to accept inadequate security practices, particularly for organizations handling sensitive data. The message resonates clearly: data protection represents not merely a compliance checkbox but a fundamental business imperative.
Looking toward 2026, organizations face both challenges and opportunities. The threat landscape will continue intensifying with AI-powered attacks, sophisticated phishing campaigns, and expanding attack surfaces from remote work and cloud adoption. However, the lessons from 2025 provide a roadmap for protection. Implementing Zero Trust architecture, mandating multi-factor authentication, strengthening vendor management, deploying comprehensive encryption, and fostering security-aware cultures will dramatically reduce breach risk.
Protection requires commitment at every organizational level. Security cannot remain solely an IT concern, it demands executive leadership, board oversight, adequate budget allocation, and employee engagement. The organizations that weather future attacks most successfully will be those viewing cybersecurity as continuous investment rather than episodic expense.
The financial stakes are immense, with average breach costs exceeding $4 million and regulatory penalties reaching into hundreds of millions. However, the reputational damage often proves even more costly. Customer trust, once lost through a data breach, requires years to rebuild, if it can be recovered at all.
As we enter 2026, the question is not whether your organization will face cyber threats but how well prepared you'll be when attacks occur. The choice is clear: invest proactively in robust security measures, comprehensive employee training, and proper vendor oversight, or risk becoming another cautionary tale in next year's breach reports.
Take Action Now with Regulance. Contact Regulance today to schedule your free consultation and discover how our platform can strengthen your security posture, ensure regulatory compliance, and protect your most valuable asset: your data.
The breaches of 2025 taught us invaluable lessons. Let 2026 be the year your organization moves from reactive to proactive security before becoming the next headline.